A web portal is a website or service that acts as a point of access to information from the World Wide Web. Web portals often have personalized features such as email, news, stock prices, and weather. Moreover, it may also provide access to other websites and services such as online forums and databases. Some examples of web portals include EACS, Yahoo, MSN, and AOL. Let’s have a look at all the details of the EACS web portal that you should consider.

The Best Steps to Improve Website Security:
Securing data through the use of a web portal involves several key steps:
- The first step is to enable two-factor verification.
- Keep an eye on regular updates to resolve security issues.
- Regularly back up important data to avoid data loss in a security breach.
- Select the web portal launched with Windows 95
- Make use of a web application firewall (WAF) to protect against common web-based attacks.
- Check the portal for the malware activity and have a response plan in case of a security incident.
It’s also important to note that security is an ongoing process. Also, regularly review and update your security measures to ensure that your Ecobee web portal is secure.
The best Steps for Website Security:
Below are some of the steps you should take to enhance the system’s security.
Select a Smart Password:
To choose a strong password for website security, it is recommended to use a combination of uppercase and lowercase letters, numbers, and special characters. The password should also be at least 12-15 characters long. It’s also a good idea to use a different password for each website or account. The password can be helpful for you to manage the workflow with ease.
Record User Access:
To record user access on the EACS web portal, you can use a combination of techniques, including:
Logging:
Keep track of all login and logout attempts, as well as any other relevant activities, such as file access or system changes.
Auditing:
Use audit trails to track who made changes to system files or data, and when they were made.
Access Controls:
Use permissions to restrict access to sensitive information to only those who need it.

Two-Factor Authentication:
Add an extra layer of security by requiring users to provide a second form of verification, such as a fingerprint or text message code, in addition to a password. Also, it is important to regularly review and analyze your tenant’s web portal to detect any suspicious activity and take appropriate action. Additionally, it can provide features like two-factor authentication, IP restriction, and many more which can strengthen the security of the website.
Using Secure Web Host:
To use a secure web host for data security, you should look for a host that offers the following features:
SSL/TLS Encryption:
It encrypts all data transmitted between your website and its visitors, making it unreadable to any third parties who might intercept it.
Regular Backups:
Your web host should regularly back up your website’s files and databases to protect against data loss.
Firewall Protection:
A firewall can help to protect your website against hacking attempts and other malicious traffic.
Regular Software Updates:
Your JCSU web portal should keep all software up to date to ensure that any security issues are patched as soon as they are discovered.
Access Controls:
You should have control over the user access to your hosting account, and the ability to grant and revoke access as needed.
Compliance Certifications:
Look for web hosts that have compliance certifications, such as SOC 2, PCI DSS, and HIPAA, which are designed for protecting sensitive data.
DDoS Protection:
Distributed Denial of Service (DDoS) attacks can overload your server and make your website unavailable. Therefore, a web host should have DDoS protection in place to prevent this type of attack. Thus, always ensure that your web portal launched with Windows 95 is safe and ideal.
24/7 Support:
A good web host should offer around-the-clock customer support so that you can get help if you have any security concerns or issues. Moreover, it’s important to note that you have a secure website and not just a secure host.

Backup Your Website:
There are several ways to back up a website, including:
- Use a plugin or extension for your content management system (CMS) such as WordPress or Joomla. Moreover, these plugins can automate the process of backing up your website’s files and databases.
- Manual backup using FTP (File Transfer Protocol) or SFTP (Secure File Transfer Protocol) to download all of the files on your website to your local computer.
- Prefer a website backup service provided by your hosting company, which can automatically create backups at regular intervals.
- Use a version control system such as Git to track changes to your website’s files and allow you to easily revert to previous versions if needed.
- Utilizing cloud backup services like AWS S3, Google Drive, Dropbox, etc.
It is important to note that you should back up all files and databases regularly, and store the backup in a safe place. Also, you should test the backup in the EACS web portal to ensure that it can be restored successfully.
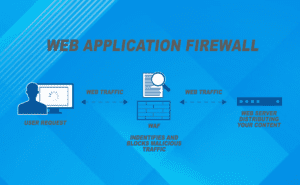
Web Application Firewall:
To apply for a web application firewall (WAF), you will typically need to follow these steps:
- Research and choose a WAF provider that meets your specific needs and budget.
- Sign up for the WAF service and create an account.
- Configure the WAF according to your preferences and the specific requirements of your web application.
- Deploy the WAF by integrating it into your web application’s infrastructure. Also, it may involve updating your DNS settings or configuring your load balancer to route traffic through the WAF.
- Test the WAF to ensure that it is properly protecting your web application and not blocking legitimate traffic.
- Continuously monitor the WAF’s performance and make adjustments as needed to ensure that it continues to provide effective protection for your web application.
Final Talk:
The EACS web portal can be used for website security as it is the ideal solution. Moreover, it allows for the centralization of security controls and management. It means that all access to the website can be controlled and monitored through a single portal. Thus, it becomes easier to identify and address security threats. Selecting the right software development Services Company is one the matters of great concern. If you are about to choose a development company, Jaxel is the right place for you. Moreover, we have an experienced and professional team and they can offer the best technology consulting. Connect to Jaxel for the best software development services.
Learn More:
4 Pillars for a great cloud security strategy
Top 7 Benefits of Custom Website Development
Contents